Your Data, Your Rules
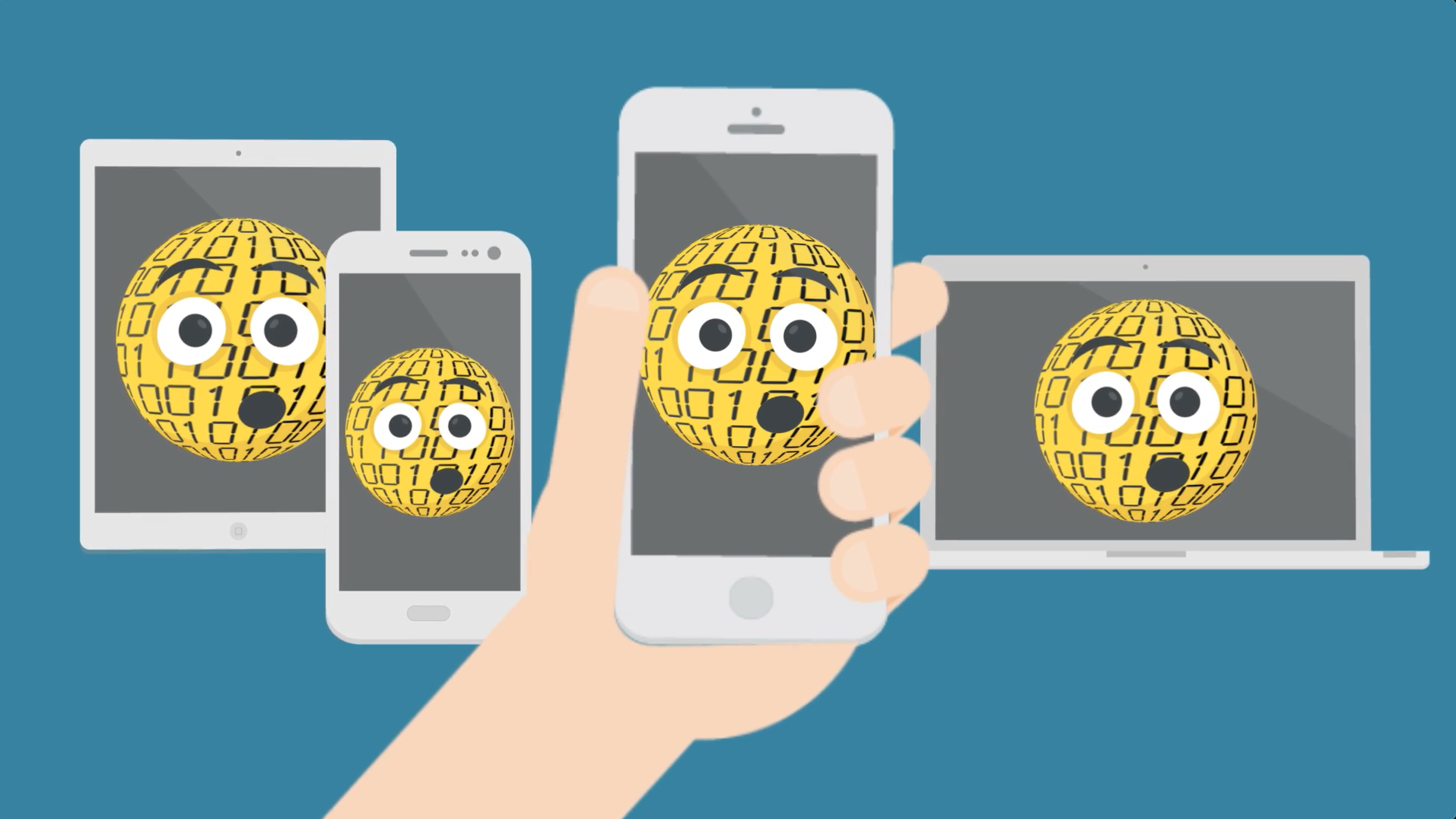
The traditional approach to data security doesn’t protect data, it guards the places where data resides. Network defenses wall off the data center. PC fortifications deter malware attacks. Encrypted tunnels protect data in motion. But when data leaves the perimeter or perimeter measures fail, the data itself remains vulnerable.
No longer.
Absio technology enables applications to build self-defending, self-directing data. By putting easy-to-use yet highly advanced cryptography tools in the hands of developers, Absio empowers software programmers to apply persistent data protections to any data created in or processed by their applications.
And because the control features are applied directly to the data object, the protections follow wherever that data goes.